

Interesting, but that does not help because Mint jails all their docs in Cloudflare.


Interesting, but that does not help because Mint jails all their docs in Cloudflare.


Also worth noting that #Ubuntu and #Mint both moved substantial amounts of documentation into Cloudflare (the antithisis of the values swiso claims to support). I have been moving people off those platforms.
BTW, prism-break is a disasterous project too. You know they don’t have a clue when they moved their repo from Github.com to Gitlab.com, an access-restricted Cloudflare site. There are tens if not hundreds of decent forges to choose from and PRISM Break moved from the 2nd worst to the one that most defeats the purpose of their constitution.
It might be useful to find dirt on various tech at prism-break, but none of these sites can be trusted for endorsements.
The prism-break website is timing out for me right now. I would not be surprised if they were dropping Tor packets since they have a history of hypocrisy.


If you look in their bug tracker, it actually reveals that they ignore dirt that has been dug up on their suggestions.


As others have mentioned there is little in the way of justification for these suggestions, and while I happen to agree with plenty of them, I’d personally like to see more reasoning, if not to appease people that already have opinions then to help newer users understand their options.
Indeed. In fact it’s actually worse than you describe. Swiso witholds negative information. They don’t want to inform people. They want to steer people. For example, swiso’s endorsements for donation platforms have some quite serious problems:
https://codeberg.org/swiso/website/issues/141
swiso is also aware of the serious issues with Qwant and the serious issues with DuckDuckGo. Not only failing to remove them but also failing to inform. Qwant and DDG are both Microsoft syndicates!
(if anyone is interested, one of the most privacy-respecting search services is Ombrelo¹, which is largely unknown to the world because PTIO, swiso, and prism-break don’t do the job they claim to do)
And swiso is aware because that’s their bug tracker.
/cc @Imprint9816@lemmy.dbzer0.com
¹ https://ombrelo.im5wixghmfmt7gf7wb4xrgdm6byx2gj26zn47da6nwo7xvybgxnqryid.onion/


Protonmail failed to satisfy F-Droid’s inclusion criteria because it requires gms (playstore framework) and because it uses Firebase messaging.
Since I’ve disabled gms in my device I’m not sure how Protonmail would work for me. Someone tells me I might simply lose push notifications capability. But I am confused because Snikket pushes notifications just fine on my device.


I’m on the edge of quitting protonmail. The issues:

Now that Google is ending the Google Cache, archive.org is really the only service we have for archiving the whole web. This has to change.

similar study reported by the ALA. (pdf research paper which also cites PEW research center)
Interesting excerpt:
Gen Z and millennials’ high use of Amazon’s audio-book and ebook paid subscription services poses a challenge for libraries articularly because of “Amazon-exclusive” licensing, which prohibits some authors from distributing their work outside the Amazon ecosystem.

from the article:
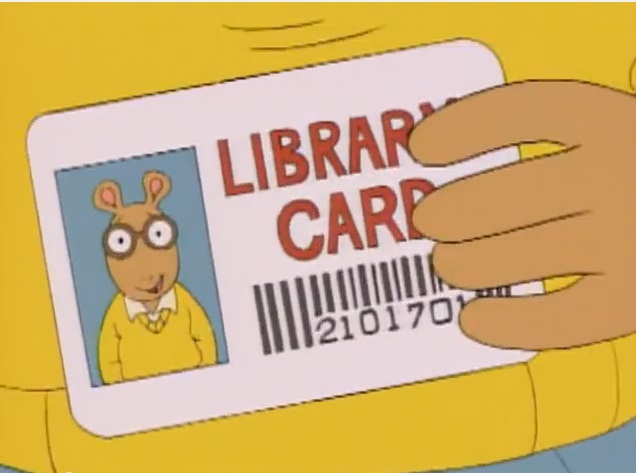
Younger generations tend to be more values driven than older ones, and libraries’ ethos of sharing seems to resonate with Gen Zers and millennials – as does a space that’s free from the insipid creep of commercialism. At the library, there are no ads and no fees – well, provided you return your books on time – and no cookies tracking and selling your behavior.
Actually we need to work on that.
Libraries do little to nothing to make browsers defensive w.r.t the intrusive web and some libraries even block Tor, which enables ad surveillance corps to monetize your data. PCs are usually all Windows (which has some baked-in surveillance) and often the systems are hardened so users cannot deploy¹ any kind of self-defense tools. Network users are sometimes blocked from using egress Tor traffic (iow, nothing that threatens the library itself). Library patrons are distrusted more than the surveillance advertisers on the other end. So patrons have to contend with both a spammy web and having their hands tied by excessive nannying.
I was unable to fetch the Debian OS at the library because the ISOs are no longer on the official mirror sites. Someone had to setup a server on a non-standard port. One particular library branch decided it was a good idea to arbitrarily block uncommon ports (WTF). And because the security was outsourced without support, the librarians were helpless.
Although to some extent these barriers might not put off millennials because they never experienced the free, open, and ad-free internet we had ~2—3 decades ago.

There are maker spaces devoted to that around the world called “fab labs” equipped with CNRs, 3d printers, welding gear, etc, but the hourly prices are insane. A library seems like the wrong place for that sort of thing but I’m sure the price is right.

I recall reading in a kbin bug (which reported that votes are public and should not be) that Lemmy votes are not. So I could have been misinformed… i did not look into it.

So everyone is stupid trying to run lemmy the way they can
Some people are more skilled than others. Skilled admins know how to avoid CF. Skilled users know how to find instances that are run by skilled admins (non-CF). Unwise users give up something for nothing and needlessly trust and empower a demonstrably abusive tech giant.
Because privacy is more important on a public forum than fighting the bots.
Of course. Privacy is about control not just security. Those bots CF fights are beneficial. The fight against beneficial bots has collateral damage on humans caught in the cross-fire, evidenced by countless discriminatory CAPTCHAs, driven by some protectionist asshole who doesn’t want their data scraped. The fight against bots is harmful to human users; not just because of the discrimination against blind people but also because we lose the benefits that beneficial bots bring us.
But someone for some reason should give you a server for free. … So you won’t contribute, won’t help just nag about everything. ok.
Of course. Money isn’t free. Your expectation that a developer not only contribute labor to the commons but also spend their own money is a perversely absurd demonstration of self-entitlement. If you want a tor version make it yourself and use the high-speed connection you already have to test with.
But you CAN solve the issues of lemmy because you CAN fork it, but you won’t.
Fork it for what purpose? Adding Tor support is useless on a capped uplink.
You trust some random guy from Finland more than everyone else,
Citation needed. I’ll trust any random person more than Cloudflare because CF has proven to be untrustworthy.

When running an instance, everything i follow or subscribe to would be fetched. A server is not going to wait until a user requests a specific article. The timeline will be populated and mirror everything – more than I would likely read. Lemmy is designed so the timeline is populated and visits to articles are instant. I do not read every single article in any community. As an end user, my client only fetches content I under my micro-control.
If there is a gratis VPS somewhere, I would be keen… that would open up more options.

Can you? Why don’t you have your own lemmy server and lemmy fork? I’m really curious now, if everything is so terrible here.
I do not have the kind of uplink that can handle that volume.

Ok so cloudflare can see my password hash
No, not the hash. The hash is only marginally sensitive. CF sees your /unhashed/ password (that is, your password before hashing).
everything else is the same as you,
Not at all. Cloudflare /only/ sees my public content, nothing that I listed as non-public. Of course that can change if Sopuli would suddently decide to use cf.
I can live with that if it helps the instance admin manage his free work.
Several instance admins have managed to offer their gratis service /without/ the Cloudflare compromise. So you’ve made a needless compromise in support of a harmful actor.
Afaik CGNAT shouldn’t be a problem by itself.
CGNAT users hit the blockade unpredictably. Cloudflare is anti-bot (that also includes beneficial bots). So if someone is perceived as running a bot on your network CF will either blackball the IP address or the whole range. You could then receive that blackballed IP address.
I know images are not synced to your instance,
There are many reasons why accessing the original post is useful. Images is indeed one of the problems with CF.
Federation is not supported on Tor:
In the free world of FOSS, we are not limited to what is “supported” because people can grab the code and support themselves. There is in fact a fedi client that shakes free of the server and directly accesses servers needed to assemble a thread. This tool was designed to resist fedi politics. It would naturally be blocked when accessing CFd servers over Tor. CF is just another case where a philosophically dubious configuration by a reckless profit-driven corp causes unforeseen collateral damage to human beings and broke the decentralization of the fedi with a purpose-defeating outcome. The fedi was designed for decentralization but obviously a gross oversight that a majority of fedi users are centralized on CF.

Can cloudflare see this? I don’t know how it is important?
You have to decide for yourself what’s important and who to trust. What you should consider though is that by choosing a Cloudflare instance, you needlessly overshare; you extend trust when you don’t need to which is a bad default policy. And you are trusting a massive singular tech giant who also has visibility on ~20-25% of all other web traffic in the world.
I can see the SSL cert of lemm.ee is not from cloudflare, so they can’t see https traffic.
It’s impossible for end users to know whether Cloudflare has a TLS private key. It’s also very rare for Cloudflare not to have the key because it would defeat the purposes admins use Cloudflare for. If Cloudflare cannot see the traffic, it cannot respond to requests and the full load must be redirected to the source host (thus DoS protection and performance benefits are effectively gone). The rarely used option for a web admin to not share their key with Cloudflare is only available to premium customers, which keeps the option rare.
Do you know irl, personally who is the admin of sopuli.xyz? How can you be sure that they are not run by NSA or other countries’ agents?
I cannot know, but it’s far easier to trust one entity than many entities. With lemm.ee you have a diffusion of responsibility problem (i.e. finger-pointing) if shit hits the fan… lemm.ee claims CF abused your data and CF claims lemm.ee did.
Who?
People whose ISPs use CGNAT, VPN users, the Tor community, libraries and situations of shared IP addresses in general.
You only communicate with your instance,
Not always. Sometimes I need to visit the original source. You cannot rely on 3rd party instances to keep a mirrored copy. Many instances are tight on space and when external content ages beyond a year they do a cleanup. There are also many visibility shenanigans with blocking where you realize you’re not seeing the whole conversation and need to visit original hosts to piece it together.
Which instance cannot reach lemm.ee because of cloudflare?
Any Tor instance would be inherently unable to reach lemm.ee, though I don’t know of any Tor instances myself (have not looked).

There are several ways:
curl -I "$URL" | grep -i cf-ray)Note that your instance (lemmy.dbzer0.com) is free from Cloudflare.

Every lemmy traffic is public.
Certainly not. Your unhashed password is not public. Your DMs are only normally visible to intended parties + their admins. Your IP address is only public when you interact in a generative way. Your login times and the links you visit are also non-public unless you generate content in response. Lemmy votes are also not public (unlike kbin).
NSA can just create their own instance and save everything.
No they can’t. Anyone can create an instance but that instance cannot inherently encroach on non-public data of other instances. But if the NSA is in your threat model for some reason, the NSA /can/ easily get what they want from Cloudflare and it need not even be a tailored ops scenario.
There are other services for private communication, lemmy was never advertised as one.
Disclosure is only the tip of the iceberg. Cloudflare is also a gatekeeper. When a lemm.ee user writes a post, there are several groups of people who are excluded from viewing it. Cloudflare controls which browsers people can use. CF users feed a business model that a privacy abuser profits from. There are countless problems with Cloudflare beyond the reckless disclosure problem.

The security pitfalls are far more vast on WiFi, in fact by your own suggestion: anyone in range of the library can setup their own spoofed AP. You can even be several blocks away and point a directional yagi antenna at a library or cafe to do this. It would be foolish to try this from inside the library because not only would you be in plain visible sight but the malicious traffic would be visible to the library’s admins (which in the case at hand is outsourced to Cisco). It would also be trivial for admins to detect when a new device is connected for longer than the library’s open hours.
You would have to evade the surveillance cams, ensure no trace of your identity on the router (which you would have to buy using cash), plant it using gloves so no fingerprints, and do something creative to hide it because the ports are in plain sight at waist level. If you opt to store the snooped data on the router which you then must return to fetch, that’s an insane risk that just would not justify the gains. And what do you think would be a gain that’s not possible over wifi? Even if the ethernet LAN differs from the wifi LAN, they would be configured with the same security anyway.
If someone wants to plant a malicious device in the library, wifi still makes more sense. E.g. an attacker can carve out a smartphone sized hole out of the center of a book and plant a device in a book that reaches wifi. Or if they want to power the device, there are still more options to hide it anywhere there is power, vs. trying to hide a device that must plug into an exposed ethernet port in an open room. Thus:
A Venn diagram of this would be a circle wholly inside another circle. If someone thinks otherwise, please give a viable attack scenario.
As a library user, how do I know I’m not connecting to a spoofed AP? Users are trivially safer plugging into the wall.
(BTW, if you appreciate security, you might be interested to know that your instance [lemm.ee] is a Cloudflare site; thus a US gatekeeping tech giant sees all your traffic on that instance in-the-clear. You might want to change instances. You’re welcome!)
UPDATE
They really are (excessively) on their security game – it turns out the ethernet ports are just a decoy to distract hackers from resources that actually function. Though in seriousness, we can only say they are on their security game if we scrap availability as a security objective (as non-wifi users are stuffed in this situation).
privacytools.io always was shit show even before the infighting. They put their own endorsement site on Cloudflare. The despite a collossal pile of dirt emerging on #Signal:
https://github.com/privacytools/privacytools.io/issues/779
PTIO continued endorsing Signal non-stop, refusing to disclose the issues. That was also before the breakup. Dirt was routinely exposed on PTIO endorsements and it never changed their endorsement nor did they reveal the findings on their website.
Now both factions are hypocrits just as they were when they were united. The original PTIO site is back to being Cloudflared (nothing like tossing people coming to you for privacy advice into the walled garden of one of the most harmful privacy offenders), and Privacy Guides has setup on a CF’d Lemmy node. The hypocrisy has no end with these people.